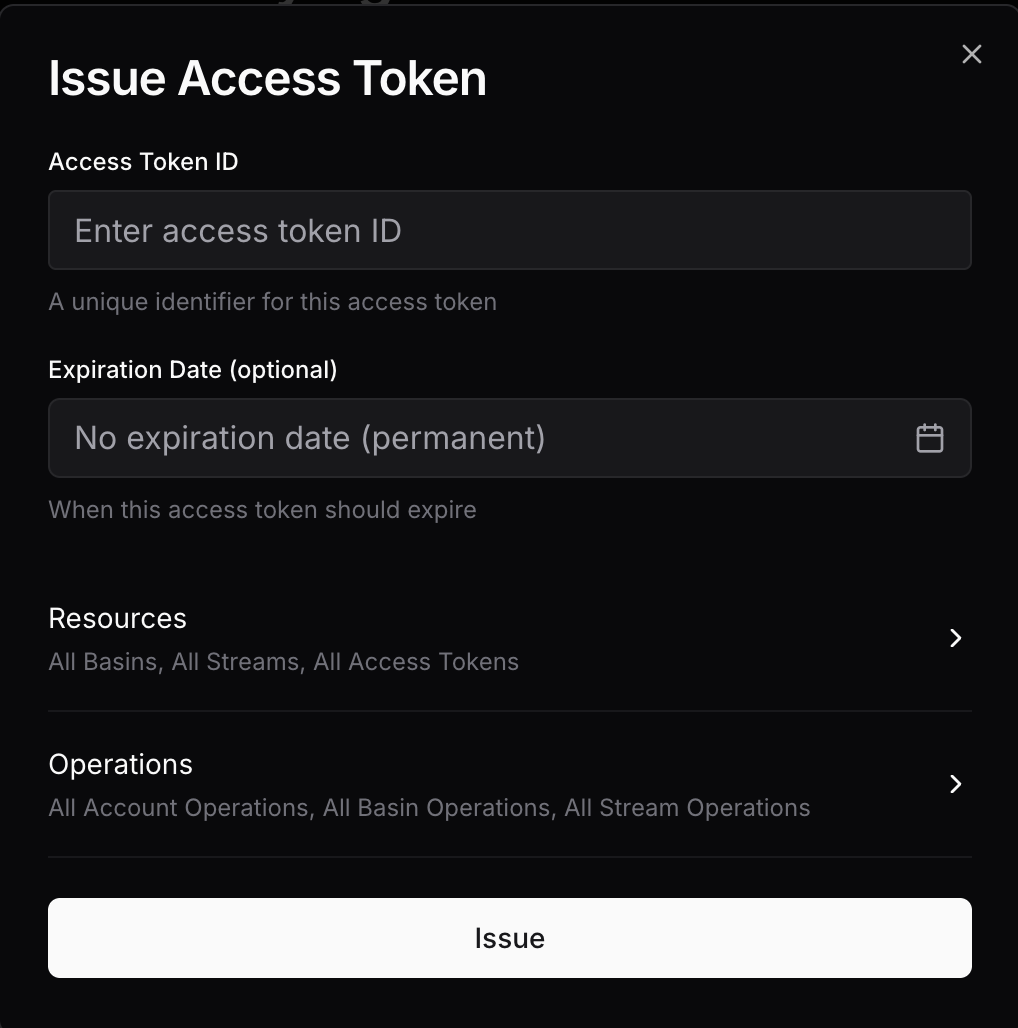
Access tokens are a first-class primitive in S2. Beyond granting administrative access, they support granular scoping — letting you issue tokens with read or write privileges tightly scoped to specific basins, streams, or prefixes. This means your users can interact directly with S2 using tokens that only expose the resources they need. Tokens are revokable and support time-based expiry. Permanent tokens work well for services; time-bound ones suit ephemeral usage like end-user sessions. There are 2 ways to list, issue, and revoke access tokens:Documentation Index
Fetch the complete documentation index at: https://s2.dev/docs/llms.txt
Use this file to discover all available pages before exploring further.
Properties
Identifier
Access token IDs must be unique to the account and may be up to 96 bytes in length.Expiration
An expiry time at which the access token becomes immediately invalid. This is specified as an RFC 3339 timestamp with the API.Expiry time of the requestor’s access token will be the default and maximum possible expiry time when issuing a new token.Dashboard access does not have an expiry, so permanent access tokens can be issued from there. However, a limited-expiry access token can be used to only issue new access tokens bounded by its own expiry.
Scope
Resources
Access to the following resources can be scoped:- Basins
- Streams
- Access tokens
- Prefix Match
- Exact Match
Grant access to all resources with a common prefix:
Empty prefix matches all resources (allow all).
Operations
There are two complementary ways to authorize operations:- Operation Groups
- Individual Operations
Operation groups provide a high-level way to grant read/write access.Group-level permissions will also apply to any new operations added to the group.
Both groups and individual operations may be specified together — the effective permissions are a union.